Privacy Fail: Blippy Exposes Users’ Credit Card Numbers
There’s been plenty of buzz about Facebook’s latest privacy changes, but social shopping site Blippy may inadvertently steal some of the concern.
Blippy.com, a site that allows users to share their purchases with friends (or the world, if they choose) based on credit card purchases, allowed some credit card numbers to remain visible through a simple Google search. {Mashable}
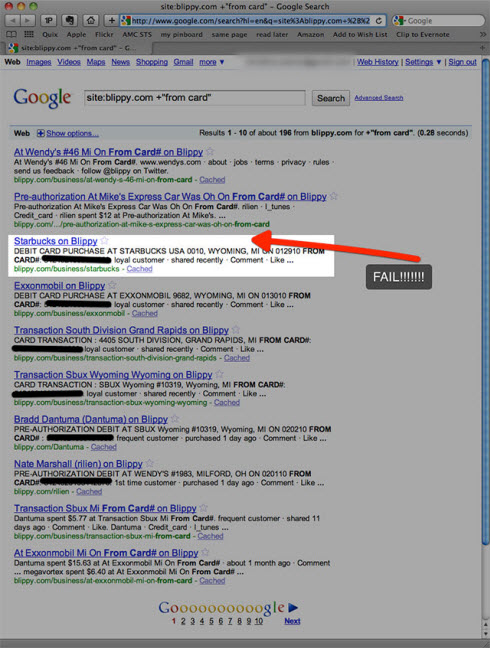
Image via Mashable.com
Nearly every major search engine – Google, Yahoo and Bing, adhere to a robots.txt file which gives directives to search crawlers on which parts of a website should be indexed or crawled in the first place. While they adhere to these guidelines in most cases, a more secure method for site owners working with sensitive data would be to restrict crawling and indexing of certain information at the server level.
“Many months ago when we were first building Blippy, some raw (not cleaned up, but typically harmless) data could be viewed in the HTML source of a Blippy web page. The average user would see nothing, but a determined person could see “raw†line items. Still, this was mostly harmless — stuff like store numbers and such. And it was all removed and fixed quickly.
Enter Google’s cache. Turns out Google indexed some of this HTML, even though it wasn’t visible on the Blippy website. And exposed four credit card numbers (but a scary 196 search results).”
Here’s the thing, Blippy is backed by some of Silicon Valley’s biggest investors. Ron Conway (an early Google investor), Philip Kaplan (AdBrite founder), Evan Williams (Twitter co-founder) and Sequoia Capital (the firm that’s funded Google, Apple and countless other tech giants). The company was started by two Stanford Computer Science grads.
Between all those connections, no one understood enough about search engines to prevent sensitive data – even if a small amount, from being included in a public index? Or thought to hire someone familiar with search engine optimization and indexing or security to at least make best practice recommendations?
Doing a site search, and viewing the source code of a web page aren’t exactly cutting edge hacking skills. In most cases, what people will find is harmless – notes on scripts used to give a website certain effects, comments made as changes are being made, etc. But leaving identifiable financial data exposed in non-secure areas – even if not plainly visible, is just plain sloppy.
